What “MFA Everywhere” Misses: Closing the Gap Across Service Accounts, Admin Protocols & Legacy Apps
Published March 23, 2026

Identity has become the primary attack surface – playing a material role in nearly 90% of cyber incidents. Amid rising identity security risks, multi-factor authentication (MFA) adoption rates now average 87% in large enterprises.
But most disruptive cyberattacks aren’t just a product of unchallenged initial access – they escalate due to unchecked lateral movement and implicit trust inside the network. While widespread MFA adoption theoretically protects organizations against rising identity threats, the reality is that common attack paths and critical systems often remain exposed.
We’ll explore what it truly means to apply MFA everywhere, why traditional MFA solutions leave critical protection gaps, and how security teams can ensure service accounts, administrative protocols, legacy apps, and other tough-to-secure assets are adequately covered.
Traditional MFA Security Gaps: How Real Attacks Unfold
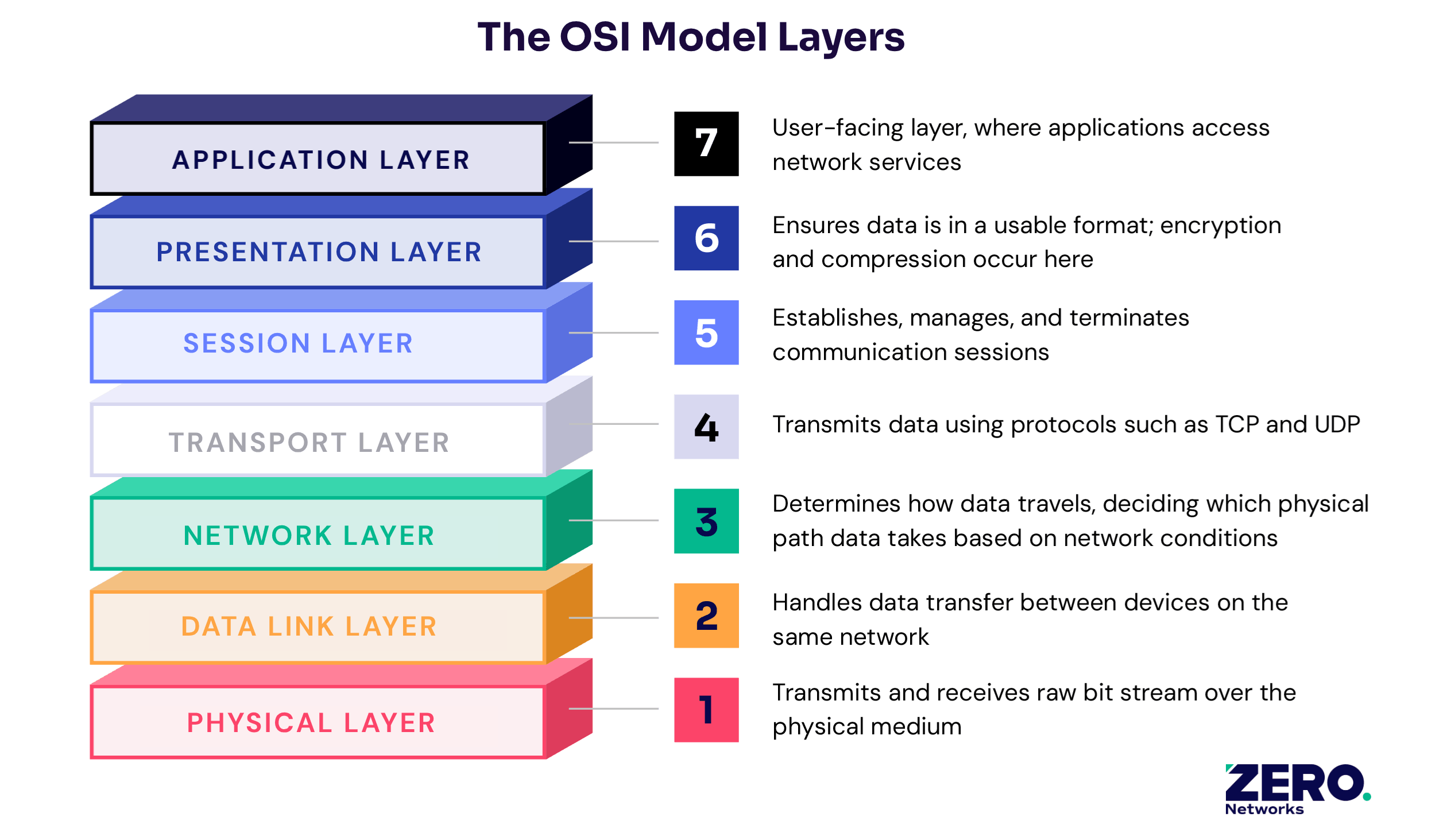
Conventional MFA operates at Layer 7 of the OSI model – the application level. While this strategy effectively protects SaaS applications and web portals, it leaves privileged ports and protocols, legacy systems, and other non-SaaS assets operating below Layer 7 unprotected.
 Because this is the standard approach for MFA, when security leaders talk about applying “MFA everywhere,” they usually mean protecting login portals, cloud apps, VPN gateways, and email platforms. In other words, governing authentication at the entry point into an application without determining what happens inside the network, after initial access.
Because this is the standard approach for MFA, when security leaders talk about applying “MFA everywhere,” they usually mean protecting login portals, cloud apps, VPN gateways, and email platforms. In other words, governing authentication at the entry point into an application without determining what happens inside the network, after initial access.
But as the 2026 Unit 42 Global Incident Response Report points out, identity isn’t just how attackers gain an initial foothold – it’s also how adversaries escalate minor incidents into high-impact breaches while the expanding identity attack surface gives threat actors more room to operate.
There’s a structural gap between where MFA enforcement stops and attackers’ movement begins.
Most enterprise risk today isn’t driven by sophisticated exploits or novel zero days that enable initial access. Instead, threat actors rely on valid logins and normal, trusted access paths.
5 Security Vulnerabilities Left by Conventional MFA
Because most security breaches today escalate due to unchecked lateral movement rather than initial access, a handful of threat landscape realities create dangerous MFA security gaps for organizations that rely heavily on traditional MFA:
- Credential abuse remains the #1 initial access vector: The idea that MFA blocks 99% of identity-based attacks only tells part of the story. Today, most attackers don’t break in – they log in. When attackers exploit valid credentials, MFA only blocks 1.5% of adversary attempts since traditional MFA solutions often don’t take factors like device and identity context into account.
- 71% of threat activity flows through four admin protocols: SMB, RDP, WinRM, and RPC are high-trust highways for IT operations – they’re also lateral movement thoroughfares, exploited by cyber adversaries across more than 70% of threat activities.
- A single compromised system gives attackers access to 85% of the environment in one hop: Overly permissive internal access makes it easy for attackers to quickly expand reach and escalate privileges, reaching critical systems and disrupting the business. In fact, an analysis of more than 680,000 identities found that 99% of cloud users, roles, and services held excessive permissions – often unused for 60 days or more.
- Machine identity and service account sprawl: Machine identities (like service accounts and API tokens) now make up over 70% of networked identities – particularly concerning since these accounts are notoriously overprivileged and under-monitored. For example, just 2.6% of workload identity permissions are actually used, and 51% of workload identities are completely inactive. This problem is only growing more pronounced in the AI era, where AI agents inherit excessive privileges and make it even harder to discern legitimate activity.
- Legacy apps create an orphaned attack surface: From databases and OT infrastructure to custom internal tools and beyond, legacy systems typically can’t be onboarded to an identity provider and don’t support modern authentication protocols, excluding them from MFA coverage.
How Can Security Teams Block Identity-Based Attacks? A 4-Step Playbook
Addressing the fundamental network security vulnerabilities left by traditional MFA requires rethinking identity protection and aligning strategies to modern threat realities rather than continuing to rely on application-layer enforcement.
CISOs looking to do more than apply another login challenge can build a comprehensive defense against identity threats by following these four steps.
Step 1: Apply Microsegmentation to Enforce Least Privilege at Scale
Minimizing blast radius and limiting the scope of breaches requires a closed-by-default architecture that restricts what assets every identity can reach once inside the network, and not just where they can enter. Microsegmentation is key to operationalizing that architecture, protecting every asset (including legacy systems) inside its own secure zone so lateral movement pathways must be explicitly defined.
Because microsegmentation creates networks where lateral movement is constrained structurally, an attacker who compromises one system can't freely pivot to the next because the access simply doesn't exist.
Step 2: Extend Granular, Identity-Based Access Controls Across the Network
Using the same fine-grain approach used to microsegment every asset, security teams must apply granular, least-privilege logic to who – or what – is connecting. The goal is to restrict access to operational need only, eliminate implicit trust, and ensure that no identity (human or machine) carries more reach than is strictly necessary.
Critically, by enforcing identity-based access controls internally on the network layer, organizations can de-escalate identity as an attack vehicle – even when adversaries are armed with legitimate credentials. To ensure comprehensive protection, controls must be applied to machine identities as rigorously as human users:
- Scope service accounts to the minimum systems and protocols required for their actual operational role; access should be based on observed behavior, not assumed requirements.
- Treat machine-to-machine communication as a policy decision, not an implicit trust relationship. Every automated workflow, backup job, and API call should be explicitly governed.
The combination of network and identity segmentation creates the framework for a resilient, self-defending architecture.
Step 3: Eliminate Standing Privileges with Just-in-Time Access
With the right architecture in place, the next lever is tightening the privilege model itself. Persistent, always-on access to privileged systems and activities is one of the most consequential structural conditions enabling modern attacks. Still, when administrative users need to perform privileged functions, a closed-by-default strategy can create operational friction without a contingency plan in place.
Just-in-time (JIT) access eliminates standing privilege by replacing persistent access grants with time-bound, purpose-bound access that expires automatically. Users and systems request access when they need it, verify their identity, receive a scoped grant for a defined window, and lose access when that window closes, removing the risk of privilege creep and further neutralizing the threat of stolen credentials – without creating operational complexity.
Step 4: Enforce Network-Layer MFA on Admin Protocols
The final step in closing “MFA everywhere” gaps is extending MFA verification to the protocol level itself. With microsegmentation defining internal pathways, identity-aware controls determining who or what can traverse those pathways, and JIT verification policies eliminating standing privileges to control when certain actions or assets are accessed, network-layer MFA makes dynamic enforcement across high-traffic, high-risk areas possible.
Rather than only prompting authentication when a user opens an application, network-layer MFA operates at layer 3 of the OSI model, triggering verification long before a session reaches the application layer – directly at the point of access.
 Practically speaking, this means that network-layer MFA makes it possible to protect protocols like RDP, SMB, WinRM, and RPC, keep privileged ports closed by default, add a verification layer to legacy systems, and ensure just-in-time access is only granted temporarily.
Practically speaking, this means that network-layer MFA makes it possible to protect protocols like RDP, SMB, WinRM, and RPC, keep privileged ports closed by default, add a verification layer to legacy systems, and ensure just-in-time access is only granted temporarily.
Together, these four steps guide CISOs to a least-privilege architecture where blast radius is constrained structurally, not by response speed, and where the implicit trust that attackers depend on has been systematically removed.
How Zero Networks Closes the Gap: Coupling Network and Identity Protection
Zero Networks intentionally built identity-based microsegmentation, where identity governs reachability at the network layer and enforcement holds up in real-world attacks, to close the security gaps left by traditional solutions.
By tightly coupling identity and network enforcement, Zero helps organizations prevent attacks, minimize blast radius, and maintain business continuity – even when attackers get inside. Zero provides immediate visibility into every identity and asset on the network, then automatically enforces adaptive, identity-aligned policies that prevent lateral movement by default.
Every connection is verified and intentional. Every asset is protected. Every identity is explicitly governed by tailored access policies. With this approach, Zero enables security teams to neutralize identity threats and strengthen cyber resilience without adding operational complexity – request a demo to learn more.
