Like many tools, BlueHound offers a wealth of use cases, some of which may not be obvious to first time users. In this short piece, we share some of the lesser-known (but very powerful!) features of BlueHound to help you get the most out of it.
For a video walkthrough on these features, check out the video below:
#1 – Automation
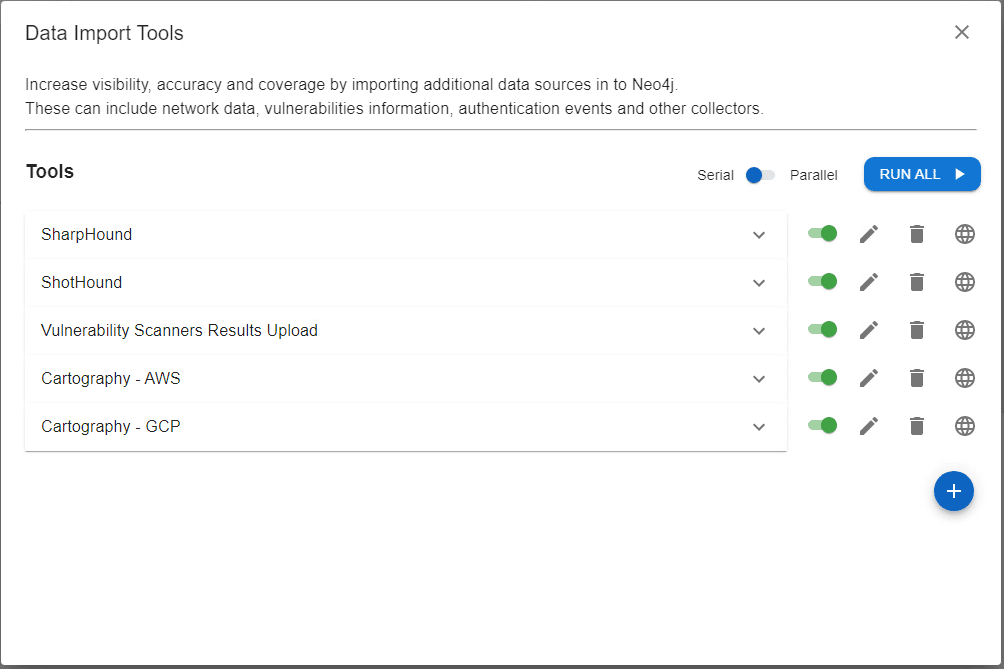
Collecting different forms of data used to mean that you needed different tools. For example, SharpHound can collect data about logged-on users, while Cartography can collect your cloud assets information. Each script needs a different configuration to work correctly, or may even need to be executed several times, and with different inputs, just to get the data you need.
With BlueHound, the process of data collection is greatly simplified. The entire cycle of collection, analysis and reporting is basically done with a click of a button. Once you have a working configuration, you can continuously run it using BlueHound to get accurate results. An upcoming version will even allow scheduling, so the entire process will execute without you lifting a finger.
#2 – Add your own data sources
Want to improve your coverage to additional environments, technologies, and/or data sources? With BlueHound, any type of data can be added and presented in the same Neo4j database.
For example, you can add IaaS information from tools such as cartography to measure the resilience of your cloud infrastructure. You can use tools such as ShotHound to add an “open” edge between hosts that have network access. Or, you can create a custom data source by integrating BlueHound with your SIEM to parse Windows authentication events, or pull information about local accounts and groups from SCCM.
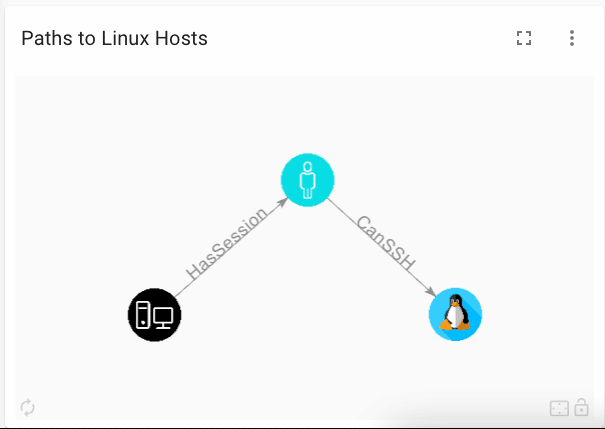
What about adding information about Linux permissions so you can have “CanSSH” and “RootOn” edges? Yep, that’s also possible.
BlueHound comes out-of-the-box, with scripts that add networking and vulnerabilities data to Neo4j, but you are only limited by your own imagination. Using the Data Import Tools section, you can add your own scripts to import data from additional sources in to Neo4j.
#3 – Measure your resilience to ransomware infection
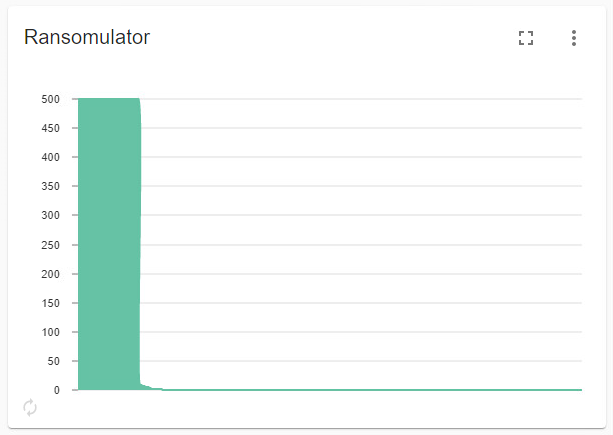
Built-into BlueHound is Ransomulator. This is a special type of chart that visualizes how a ransomware infection might spread in your environment. It does so by going over all the assets in the environment, trying to see how many other assets it can “infect”. If you are using ShotHound, or have integrated network edges in your graph, you can also run Ransomulator given the physical network access limitations.
Once Ransomulator is finished, you get a full visualization of your network’s vulnerability. In the example graph below, Ransomulator is showing the serial number of an infected host on the x-axis, and the number of other hosts that can be potentially infected via that infected host on the y-axis. This scan is completely passive and relies only on your Neo4j data, so you don’t have to worry about any risk to your network.
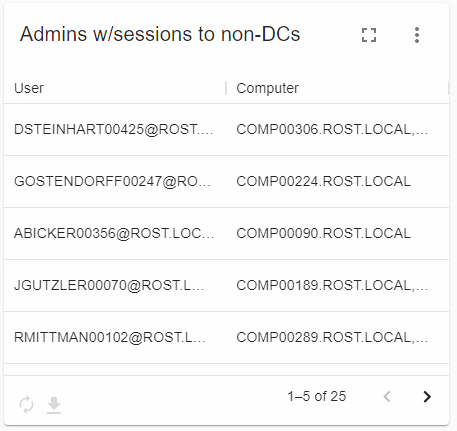
#4 – Export findings to CSV
Did you notice the small “down arrow” icon at the bottom of the table charts? It lets you save any table chart data as a CSV for further processing offline, or for handoff to other relevant teams in your company.
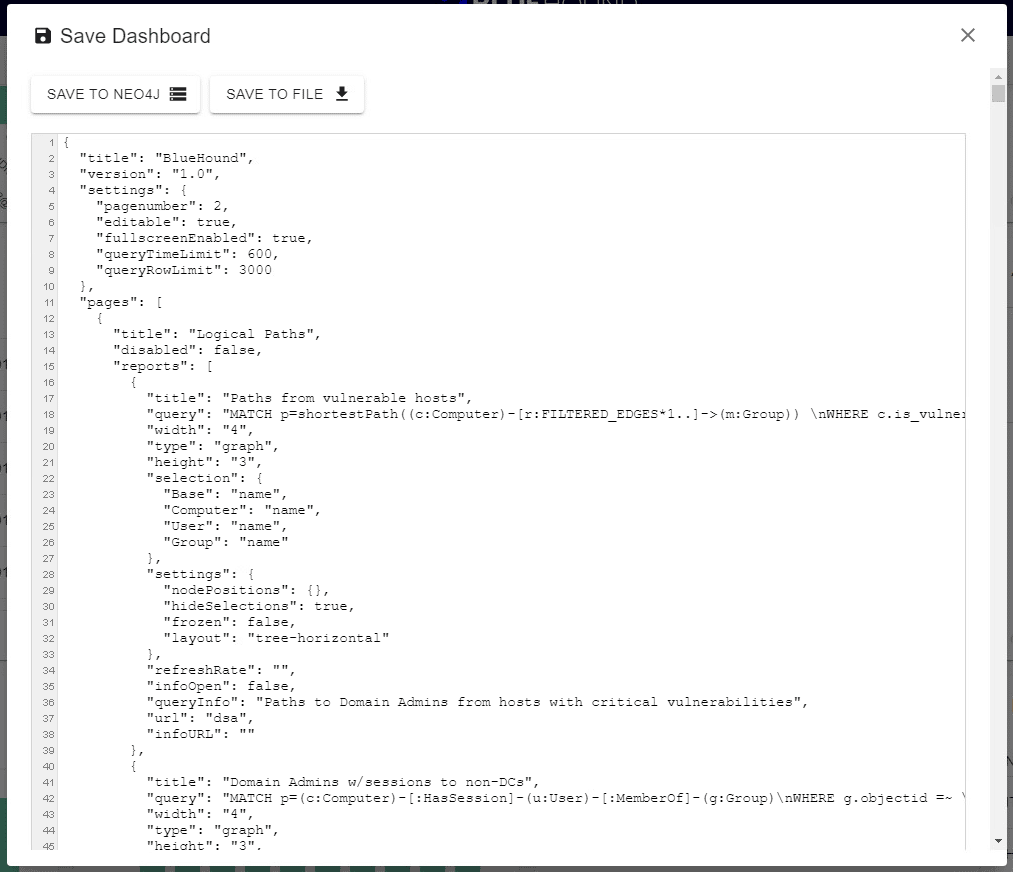
#5 – Share your dashboard & queries with the security community
Made something cool? Share it with the community! You can easily export your dashboard and queries to share with other security experts. Our strength is in numbers!
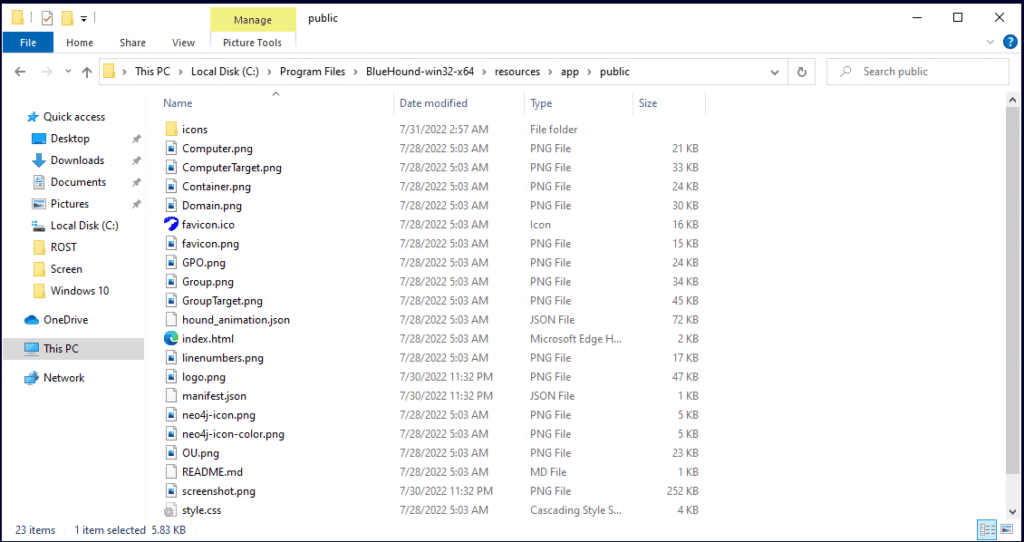
#6 – Add custom icons to your graphs
If you collect a new type of data, or simply want to freshen-up how the graphs look in the graph chart, you can do so with a simple “hack”. In your local BlueHound folder, you will find the node icons located at
Do more with your data
BlueHound is a tool designed to let you build whatever you need. Be creative, share with the community, and don’t hesitate to reach out to us if you have ideas of issues at support@zeronetworks.com.



