What is a zero day attack?
A zero day (or “0-day”) attack happens when a hacker finds and exploits a system vulnerability before the developers or owners of the system have time to fix the problem, or in some cases even become aware of it.
Zero day vulnerabilities that lead to attacks include: faulty algorithms, bugs, missing encryption or authorizations, and insufficient security measures. Because these vulnerabilities can be hard to detect, they are also hard to protect against effectively.
Of course, the small silver lining to this is that it can be difficult for hackers to find these vulnerabilities as well. The bad news? If a hacker can find and exploit a vulnerability, they can cause a lot of damage while the system owner is scrambling to build a patch, or even before they know an attack has occurred.
Why are zero day attacks a problem?
Zero day attacks can be particularly destructive because in many cases the attacker is the only party aware of the vulnerability. It can take anywhere from a few hours to a few years for system owners to catch up with the attacker and find the vulnerability that led to the attack, let alone build a patch for it. All the while, the malicious party has unfettered access to the system; they can steal data and cause a lot of damage. At other times, attackers will sit and wait for the most advantageous time to strike, which is another reason zero day attacks can be so insidious.
These attacks are a significant concern for developers and security personnel because of the difficulty of diagnosing and defending against them before major damage is done. Even after a zero day attack is detected, it can take some time for developers to investigate, develop, test, and deploy a patch, leaving unprotected systems and devices vulnerable to the attack.
Another concern is that zero day attacks are now within reach for even small extortion gangs (whereas it used to be accessible only for large players with lots of resources, like nation states). This is because of the rise in ransomware and remote work.
Zero day attack examples
- Stuxnet: This is perhaps the most well-known example of a zero day attack (it even got made into a movie!). In 2010, developers working at Siemens discovered an attack on machines running programmable logic controller (PLC) software that had been underway for 5 years. The goal was to disrupt Iran’s nuclear program, and the vulnerability that the hackers had exploited was in Siemen’s Step7 software. The bug enabled the hackers to control some assembly line machinery via the PLC software.
- Zoom: In 2020, a vulnerability in Windows 7 allowed a remote attacker to completely take over another PC running a specific Zoom version and steal files.
- Hafnium: Another example was the Hafnium attacks on Microsoft Exchange servers in 2021. This malware was able to give attackers privileged access to Exchange servers, gather information, and steal user credentials. Microsoft quickly discovered the attack but having to build and deploy a patch took much longer.
Zero day attack protection
When it comes to protecting your organization from zero day attacks, a reactive approach that relies on building patches after the attack is discovered is not good enough. Instead, organizations need to proactively prepare and be able to stop attacks from spreading. Why? One reason is that security teams are drowning in alerts. It doesn’t matter how good their methods of detection are if they’re dealing with hundreds or thousands of alerts per day. Even if they do detect a real abnormality, having the bandwidth to fully investigate it can be tough.
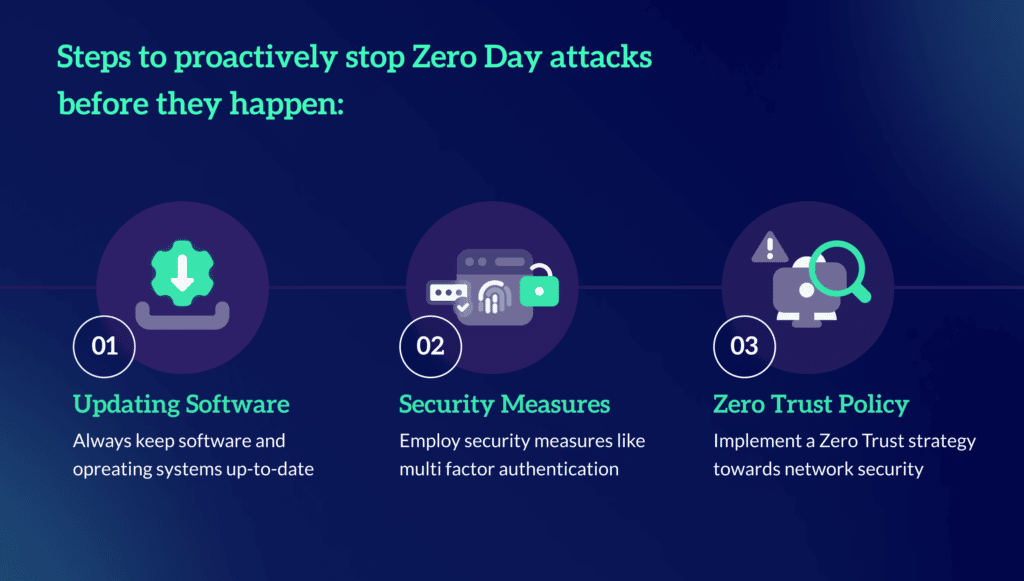
Here are some steps to take to proactively prepare your organization and stop zero day attacks before they happen:
- Always keep software and operating systems up-to-date
- Employ security measures like multi factor authentication
- Implement a Zero Trust strategy towards network security.
The Zero Networks Solution
Zero Networks offers a fast and easy way to achieve Zero Trust and protect your organization against zero day attacks. We have built a way to just-in-time (JIT) allow any network connection by microsegmenting the network at the host firewall level. What this means is that almost all network connections are not allowed. Because of that, even if there is a zero day vulnerability, the attacker won’t be able to see the port and exploit it.
Zero Networks’ solution allows normal user traffic without breaking applications and apply MFA-based JIT access for administrative access that attackers love to use. It’s believed that multi factor authentication (MFA) can stop 99.9% of attacks because the attacker needs to go through the MFA process before the network port would even be open, limiting their attack surface to… nothing. Even if they are able to breach the network, this MFA-based JIT stops attackers from spreading.
About Zero Networks
Zero Networks is solving the biggest challenge in cybersecurity: making military-grade network security available to everyone, regardless of skill, size or complexity. For years, microsegmentation has been the promised land, but could never be achieved at scale. MFA, which should be the ultimate security measure, can’t fit every service and every protocol. As a result, networks remain open from the inside, and attacker’s jobs are easy once they get into at least one machine inside the network.
Zero Networks, instead, creates a new paradigm. One that makes microsegmentation fast, easy, effective, and deployable by anyone. This modern approach is self-service and automated, eliminating the need for agents while leveraging your host-based firewall for enforcement.
Zero Networks is proud to work with companies large and small around the world, helping them protect their networks from breaches and ransomware.



