What is a security breach?
A security breach is a situation in which an unauthorized intruder or attacker gains access to a company’s network, applications, and/or data. The intruder can either be a cybercriminal or a malicious application such as malware. In both cases, the intruder employs sophisticated hacking methods to bypass security measures and reach protected assets.
Security breaches occur often and sometimes on a large scale, in both small and large companies. If a breach isn’t addressed quickly it can lead to widespread system damage and stolen data. A security breach can also result in grave financial repercussions and irreparable damage to the company’s reputation, especially when customer data is affected. There have been many examples of disastrous security breaches in recent history.
While the terms “security breach” and “data breach” are sometimes used interchangeably, there is a difference between the two. Using the metaphor of a home burglary, a “security breach” would be the part where the burglar gains access to the home, through a door that was left unlocked or by breaking a window. A “data breach,” on the other hand, would occur if the burglar then stole valuables such as cash or expensive jewelry. In the world of cybercriminals, the “valuables” are things like financial data, intellectual property, or the personal information of customers.
One of the reasons security breaches are such a concern for organizations is because in many cases, preventing security breaches also prevents data breaches.
Types of security breaches
What are the types of methods deployed by attackers as part of security breaches? Three common ones are: viruses, spyware, and malware. With these methods, the attacker will embed the malicious software in an email, an email attachment, or another type of download from the internet. When the unsuspecting victim opens the attachment, their computer gets infected (with the potential to spread to other computers in the network).
How can cybercriminals convince employees to open these emails and attachments? One way is through a tactic known as phishing, where the attacker convincingly impersonates someone from the organization, oftentimes the victim’s boss or the CEO. This fake (but realistic) email convinces the employee to either download the malicious software and/or provide sensitive information to the attacker because they believe it’s their boss or some other authority figure making the request.
Another type of security breach is known as a denial-of-service attack. In this type of attack, hackers flood a website or another port in a network with traffic, rendering it unavailable and unusable to legitimate users. Other security breach types include exploiting software bugs, using encryption software to launch ransomware attacks, or insider attacks (in which employees with legitimate access to the network steal data for their own personal gain). Edward Snowden was one of the most famous examples of an insider attack.
Causes of security breaches
Oftentimes, security breaches are caused by vulnerabilities in an organization’s security apparatus that hackers detect and exploit, but they can also result from employee error or lack of awareness.
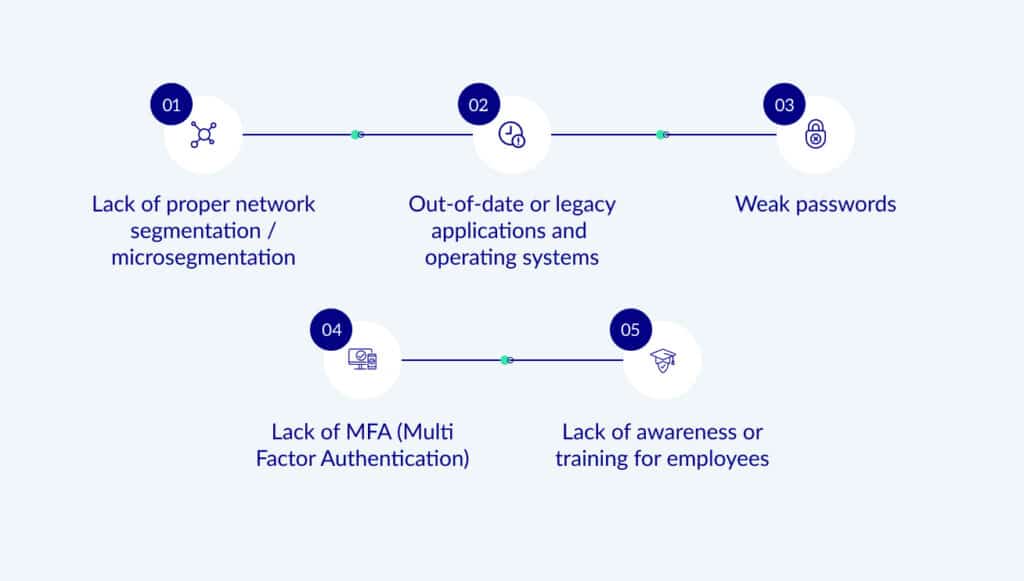
Some examples of security vulnerabilities that can lead to security breaches are:
- Lack of proper network segmentation / microsegmentation. Segmenting a network means dividing it into smaller parts that can’t communicate with each other. If done right, each asset will be its own network segment (aka “microsegmentation”). This can stop most security breaches, but it can be hard to do it properly, and at scale.
- Out-of-date or legacy applications and operating systems. Software vendors are constantly updating their products to fix vulnerabilities and bugs. Therefore, when parts of a network are out-of-date, the entire network is vulnerable to exploitation.
- Weak passwords. Passwords that are too obvious or used for multiple applications do not provide adequate protection to a network and its assets.
- Lack of MFA (Multi Factor Authentication). Even if passwords are weak, additional security can be achieved by requiring users to provide another form of authentication such as a fingerprint or access code sent to their phone. If MFA is not in place (and passwords are weak), there is little protection of your network from attackers.
- Lack of awareness or training for employees. Even the most secure network can be breached because of well-meaning, unwitting employees who are not trained to recognize and report suspicious emails or behavior. Cybercriminals are adept at tactics such as phishing: they use these tactics to broker trust with the employee, and thus gain access to otherwise secure data and other sensitive information. Training and awareness can mitigate this risk.
Examples of security breaches
What are some real-world examples of security breaches?
- Yahoo: In early 2014, a phishing email was sent to employees at Yahoo. Unfortunately, one employee fell for it and clicked on the link in the email, exposing Yahoo’s network—and sensitive user account information—to cybercriminals. The breach resulted in 3 billion user accounts being hacked.
- Facebook: In September 2018, Facebook announced that around 29 million user accounts had been compromised as part of a security breach. Vulnerabilities in Facebook’s security system left the user accounts exposed, which cybercriminals took advantage of.
- Equifax: In 2017, Equifax suffered a security breach that resulted in the exposure of personal data for 145 million Americans (including names, SSNs, and drivers' license numbers).
How to prevent security breaches
There are many strategies you can use to prevent security breaches (and therefore data breaches). Some of them include creating strong passwords (using both upper and lowercase letters, numbers, and special characters), changing them often, and never using the same password for multiple accounts. If you are a security leader at an organization, educate your employees on password best practices. Consider making them a requirement within your organization.
And since out-of-date applications are another security breach risk, always update your systems to the latest versions (and require that your employees do the same). When throwing out old computers or mobile devices, make sure to completely wipe the hard drive and create a fresh installation of the operating system if you plan to re-use the machine.
Even with all these measures in place, a hacker could still gain entry to your network via an employee who gets tricked by a phishing email. To prevent this from happening, training your employees is crucial. Encourage them to be vigilant and report suspicious emails to the proper authority.
Zero Networks’ solution
Zero Networks offers a fast and easy way to protect your organization against security breaches. We have built a way to just-in-time (JIT) allow any network connection by microsegmenting the network at the host firewall level. What this means is that almost all network connections are not allowed. Because of that, even if there is a security breach, the attacker won’t be able to spread and cause any damage.
About Zero Networks
Zero Networks is solving the biggest challenge in cybersecurity: making military-grade network security available to everyone, regardless of skill, size or complexity. For years, microsegmentation has been the promised land, but could never be achieved at scale. MFA, which should be the ultimate security measure, can’t fit every service and every protocol. As a result, networks are still open from the inside, and attacker’s jobs are easy once they get into at least one machine inside the network.
Zero Networks, instead, creates a new paradigm. One that makes microsegmentation fast, easy, effective, and deployable by anyone. This modern approach is self-service and automated, eliminating the need for agents while leveraging your host-based firewall for enforcement.
Zero Networks is proud to work with companies large and small around the world, helping them protect their networks from breaches and ransomware.



